GitHub Actions: Netflix Deployment

Step1: Launch an Ec2 Instance
To launch an AWS EC2 instance with Ubuntu 22.04 using the AWS Management Console, sign in to your AWS account, access the EC2 dashboard, and click “Launch Instances.” In “Step 1,” select “Ubuntu 22.04” as the AMI, and in “Step 2,” choose “t2.medium” as the instance type. Configure the instance details, storage, tags, and security group settings according to your requirements. Review the settings, create or select a key pair for secure access, and launch the instance. Once launched, you can connect to it via SSH using the associated key pair.
Step2A: Install Docker and Run Sonarqube Container
Connect to your Ec2 instance using Putty, Mobaxtreme or Git bash and install docker on it.
sudo apt-get update
sudo apt install docker.io -y
sudo usermod -aG docker ubuntu
newgrp docker
sudo chmod 777 /var/run/docker.sockPull the SonarQube Docker image and run it.
After the docker installation, we will create a Sonarqube container (Remember to add 9000 ports in the security group).
docker run -d --name sonar -p 9000:9000 sonarqube:lts-community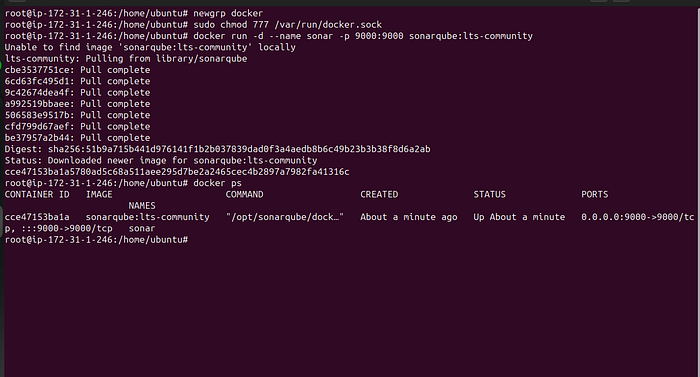
Now copy the IP address of the ec2 instance
<ec2-public-ip:9000
Provide Login and password
login admin
password admin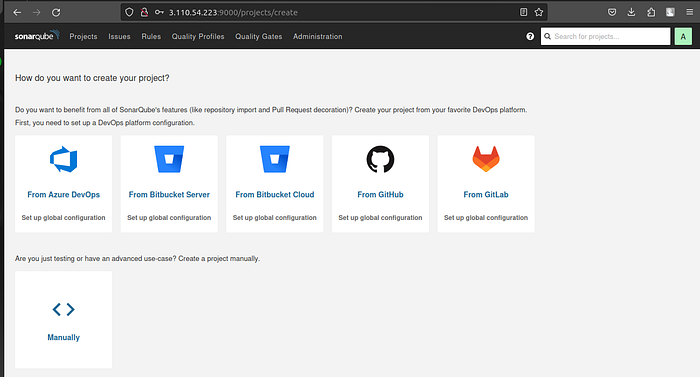
Step2B: Integrating SonarQube with GitHub Actions
Integrating SonarQube with GitHub Actions allows you to automatically analyze your code for quality and security as part of your continuous integration pipeline.
We already have Sonarqube up and running
On Sonarqube Dashboard click on Manually
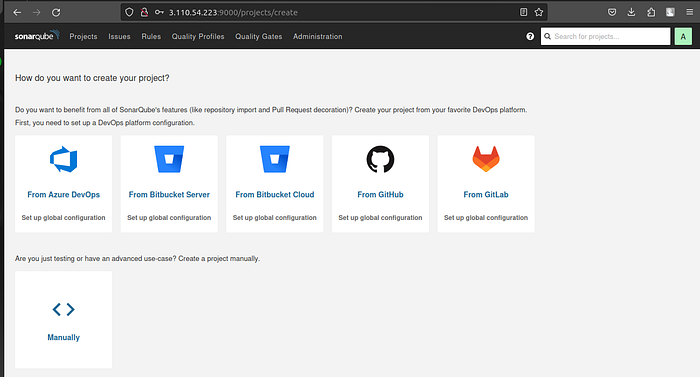
Next, provide a name for your project and provide a Branch name and click on setup
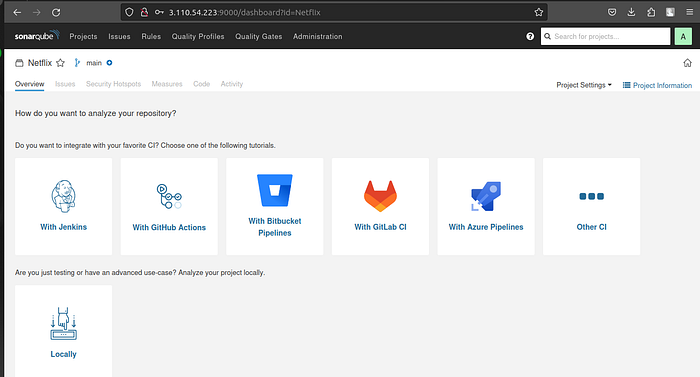
On the next page click on With GitHub actions
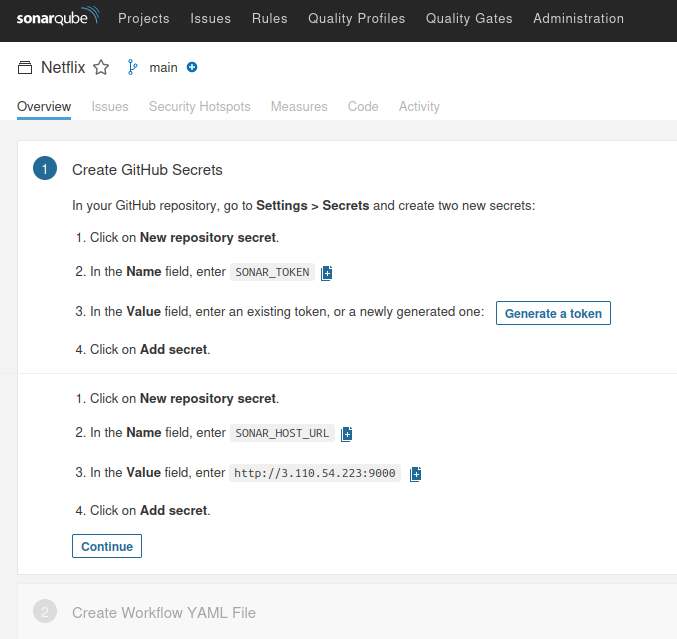
This will Generate an overview of the Project and provide some instructions to integrate
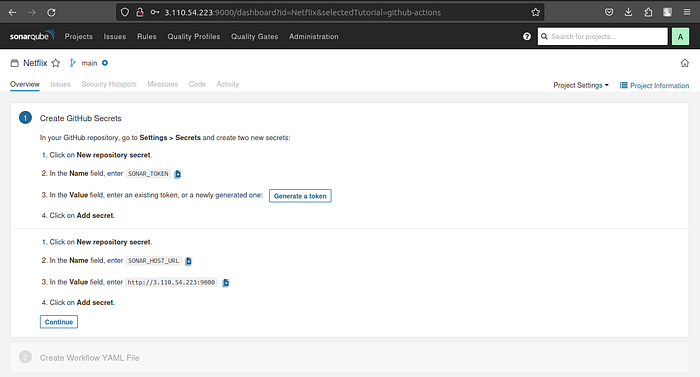
Let’s Open your GitHub and select your Repository
In my case it is Netflix-clone and Click on Settings
Search for Secrets and variables and click on and again click on actions

Now go back to Your Sonarqube Dashboard
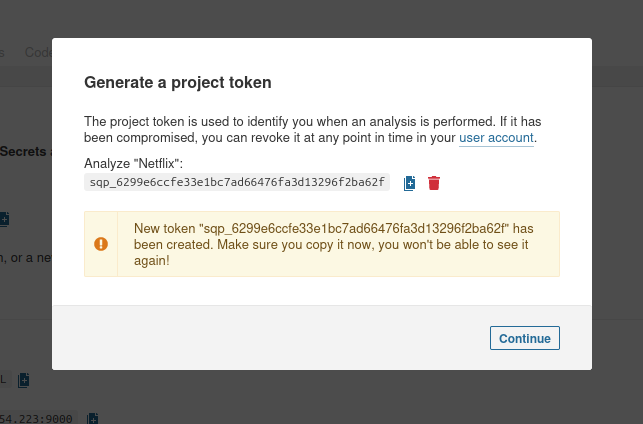
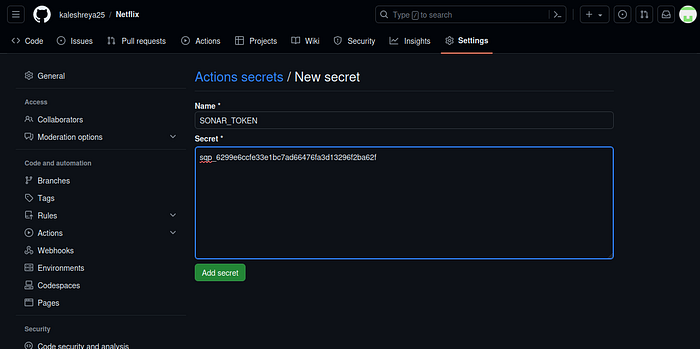
Copy SONAR_TOKEN and click on Generate Token

Click on Generate
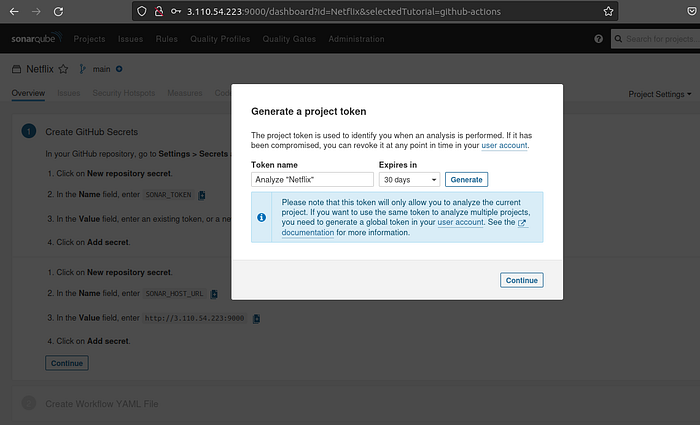
Now go back to GitHub and Paste the copied name for the secret and token
Name: SONAR_TOKEN
Secret: Paste Your Token and click on Add secret
Now go back to the Sonarqube Dashboard
Copy the Name and Value
Go to GitHub now and paste-like this and click on add secret
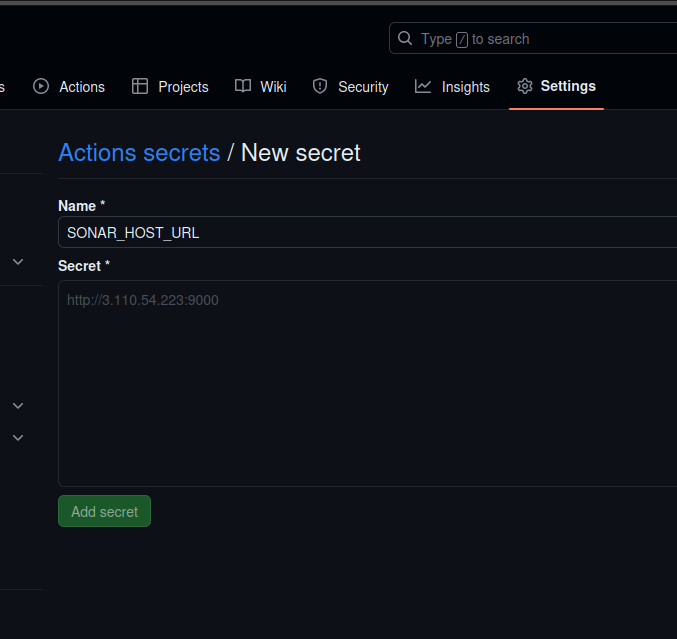
Our Sonarqube secrets are added and you can see

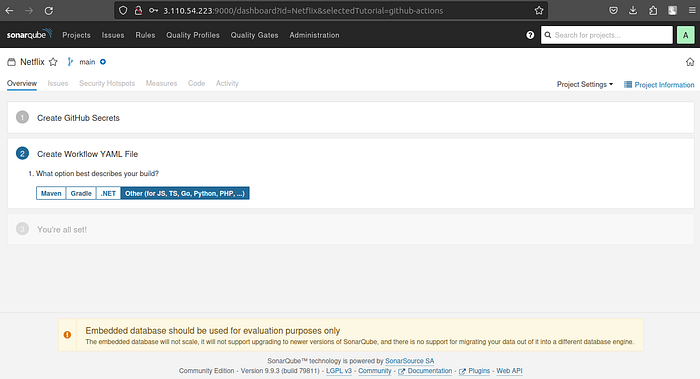
Go to Sonarqube Dashboard and click on continue
Now create your Workflow for your Project. In my case, the Netflix project is built using React Js. That’s why I am selecting Other
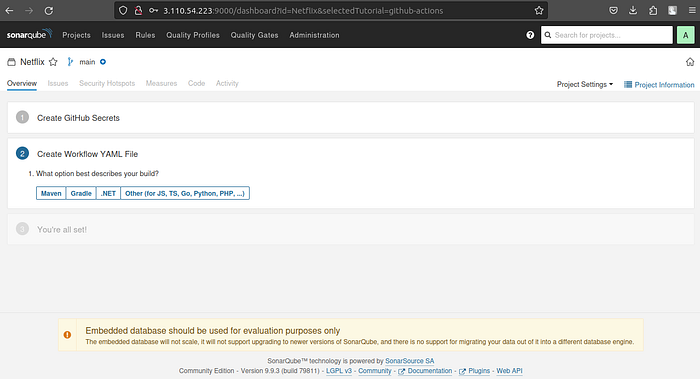
Now create your Workflow for your Project. In my case, the Netflix project is built using React Js. That’s why I am selecting Other
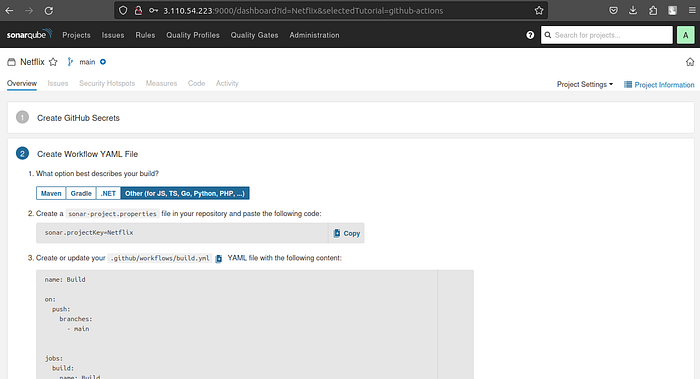
Now it Generates and workflow for my Project
Go back to GitHub. click on Add file and then create a new file

Go back to the Sonarqube dashboard and copy the file name and content

The content to add to the file is (copied from the above image)
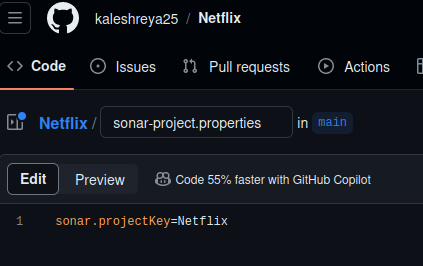
Add in GitHub like this
Let’s add our workflow
To do that click on Add file and then click on Create a new file
Here is the file name
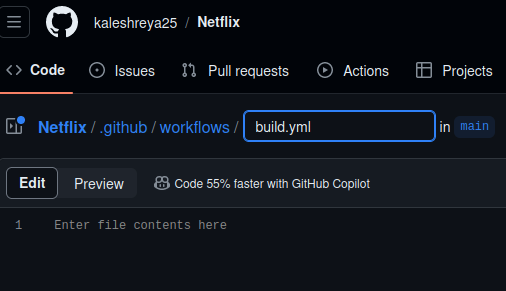
.github/workflows/build.yml 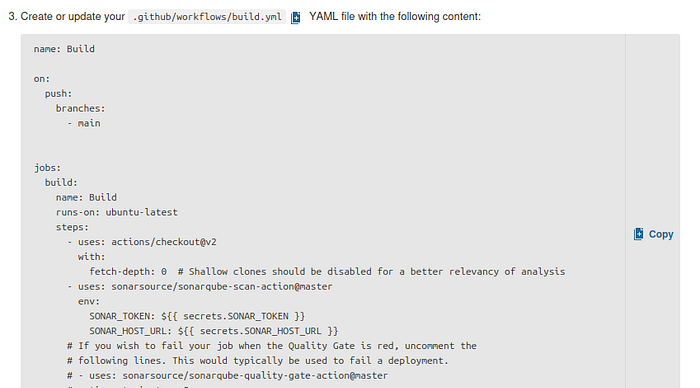
Click on commit changes
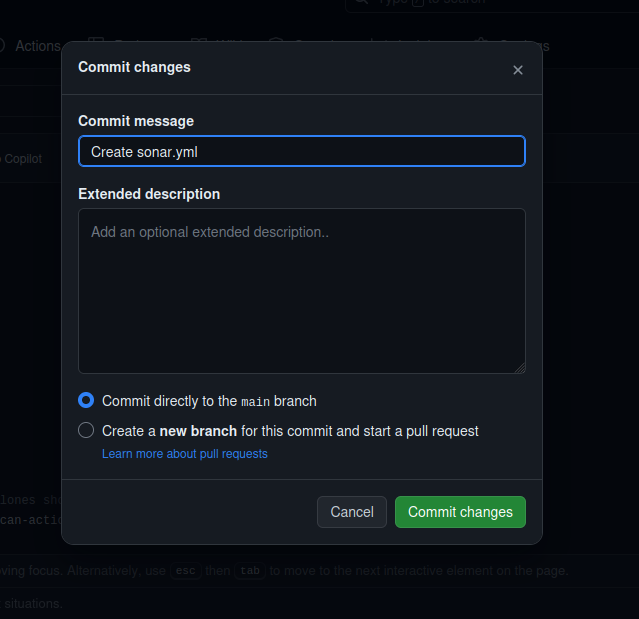
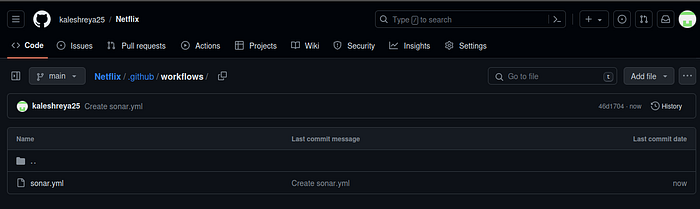
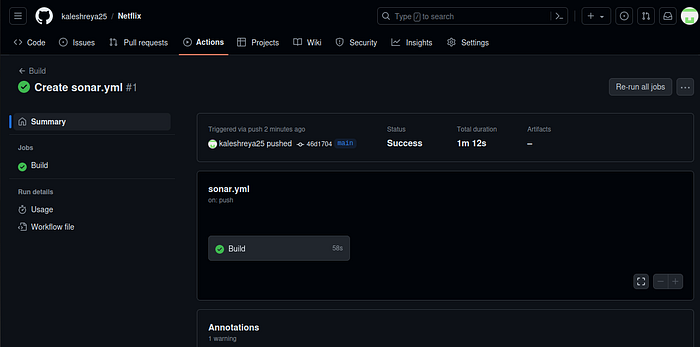
Now workflow is created.
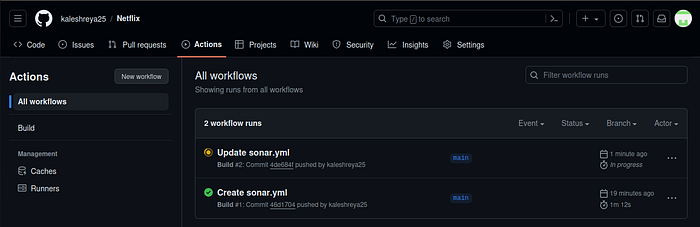
Click on Actions now
Now it’s automatically started the workflow
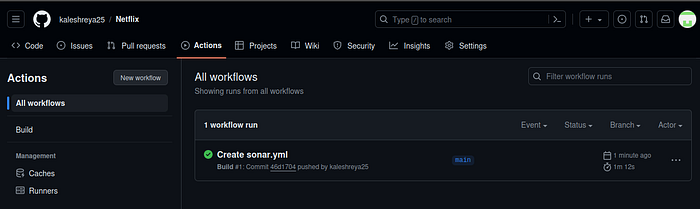
Let’s click on Build and see what are the steps involved
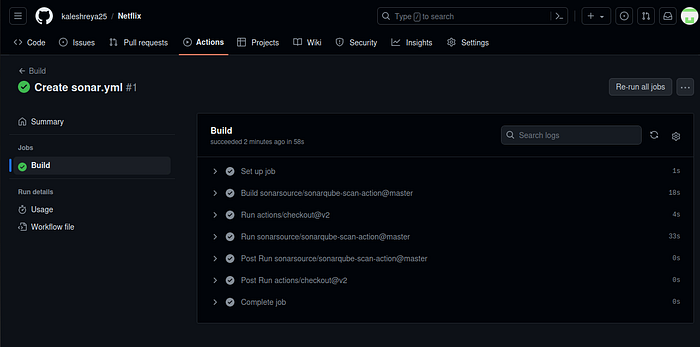
Click on Run Sonarsource and you can do this after the build completion
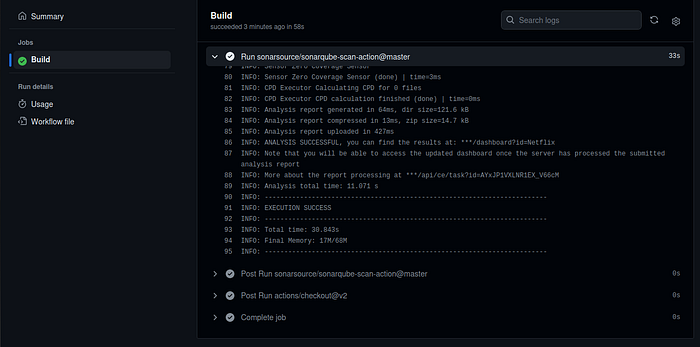
Build complete.

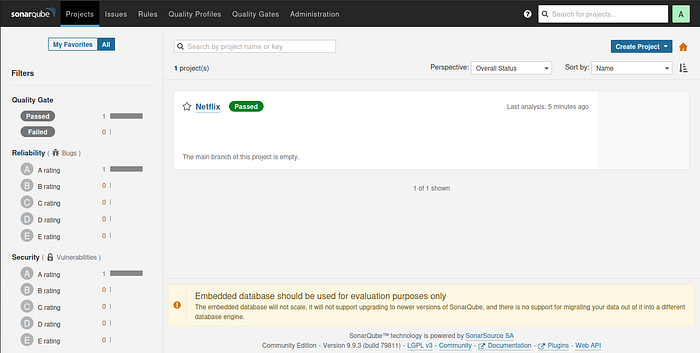
Go to the Sonarqube dashboard and click on projects and you can see the analysis
Step3: Let’s scan files using Trivy
Add this code to your sonar.yml (I mean workflow)
- name: install trivy
run: |
#install trivy
sudo apt-get install wget apt-transport-https gnupg lsb-release -y
wget -qO - https://aquasecurity.github.io/trivy-repo/deb/public.key | gpg --dearmor | sudo tee /usr/share/keyrings/trivy.gpg > /dev/null
echo "deb [signed-by=/usr/share/keyrings/trivy.gpg] https://aquasecurity.github.io/trivy-repo/deb $(lsb_release -sc) main" | sudo tee -a /etc/apt/sources.list.d/trivy.list
sudo apt-get update
sudo apt-get install trivy -y
#command to scan files
trivy fs .GitHub Actions workflow step that installs Trivy, a popular open-source vulnerability scanner for containers, and then uses it to scan the files.
Click on actions again
It started the workflow build
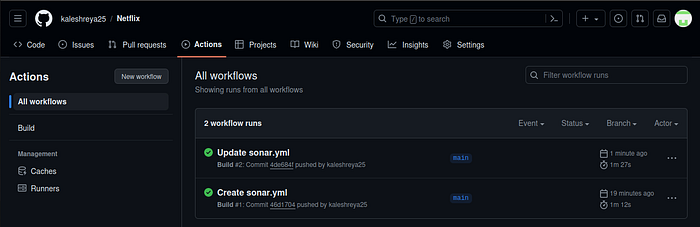
Click on Build, Analyze and scan
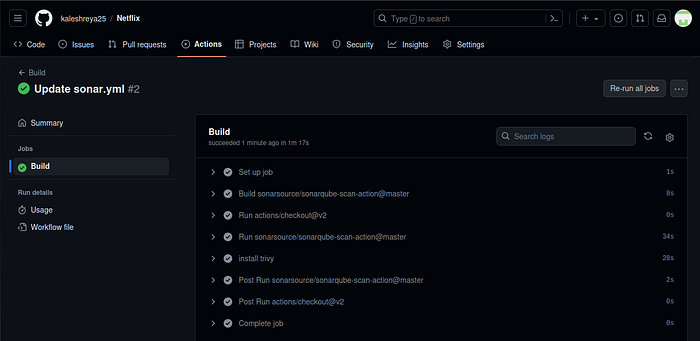
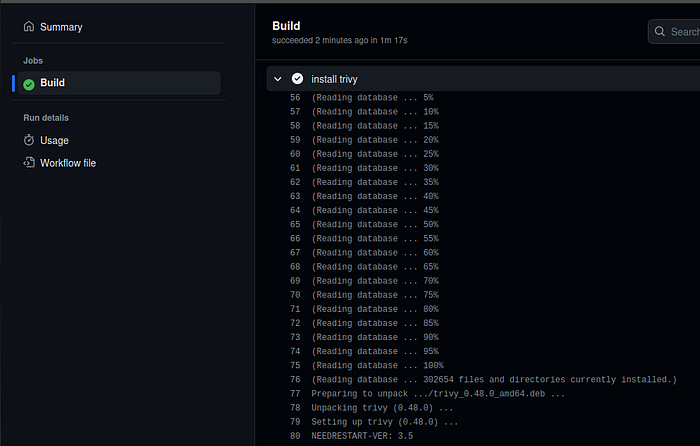
It installed Trivy version 0.48.0 and scanned files also. See report
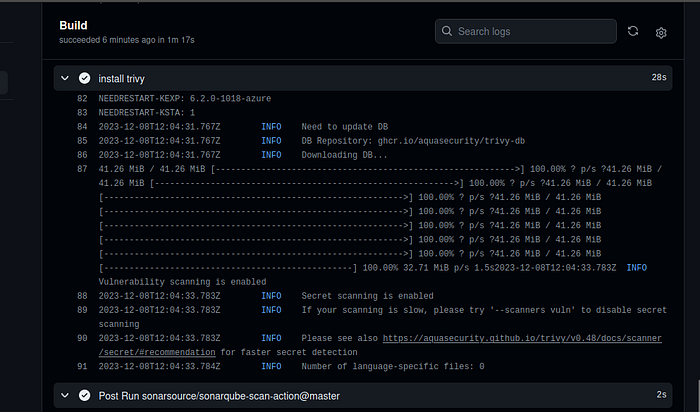
The file scan is completed, this is another security check
Step4A: Docker build and push to Docker Hub
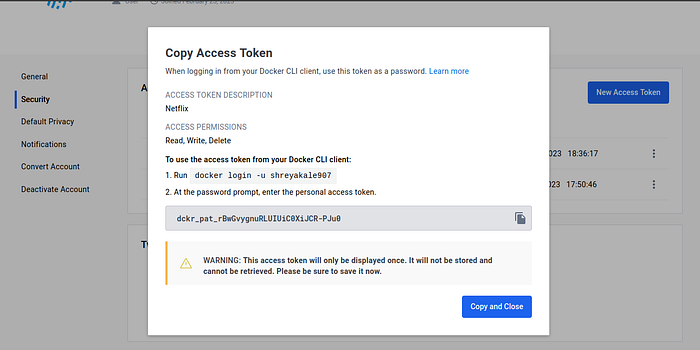
Create a Personal Access token for your Docker Hub account
Go to docker hub and click on your profile → Account settings → security → New access token
It asks for a name Provide a name and click on generate token

Copy the token save it in a safe place, and close
Now Go to GitHub again and click on settings
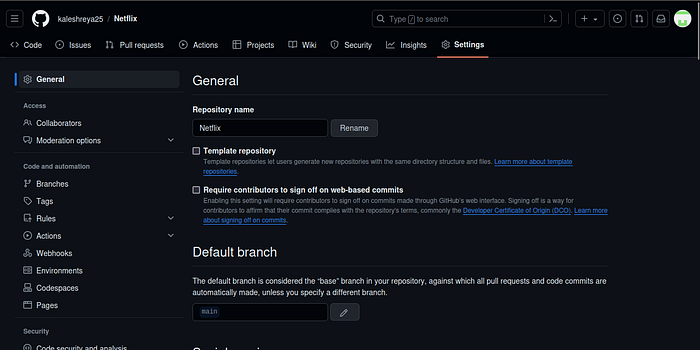
Search for Secrets and variables and click on and again click on actions
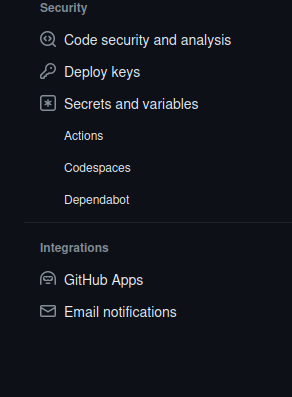
It will open a page like this click on New Repository secret
Add your Dockerhub username with the secret name as
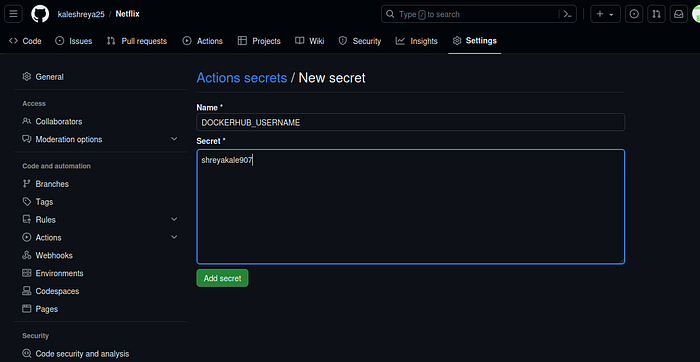
Click on Add Secret.
Let’s add our token also and click on the new repository secret again
Name
DOCKERHUB_TOKEN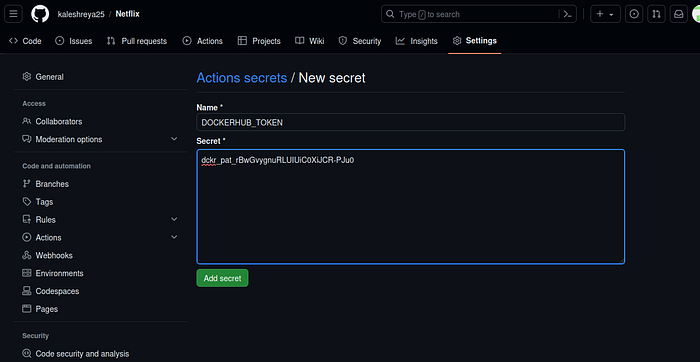
Paste the token that you generated and click on Add secret.
Step4B: Create a TMDB API Key
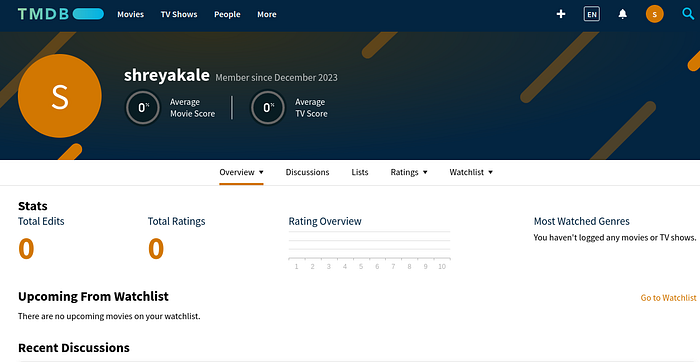
Next, we will create a TMDB API key
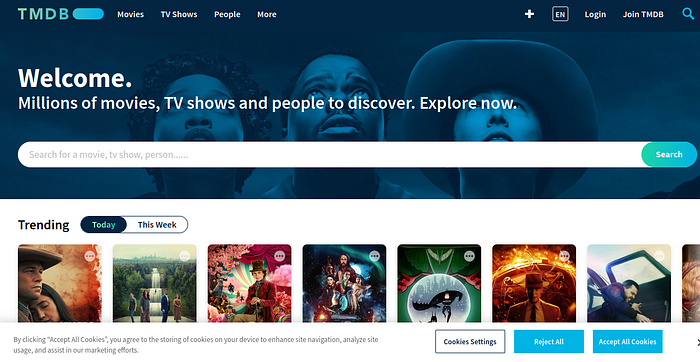
Open a new tab in the Browser and search for TMDB

Click on the first result, you will see this page
Click on the Login on the top right. You will get this page.
You need to create an account here. click on click here. I have an account that’s why I added my details there.
once you create an account you will see this page.
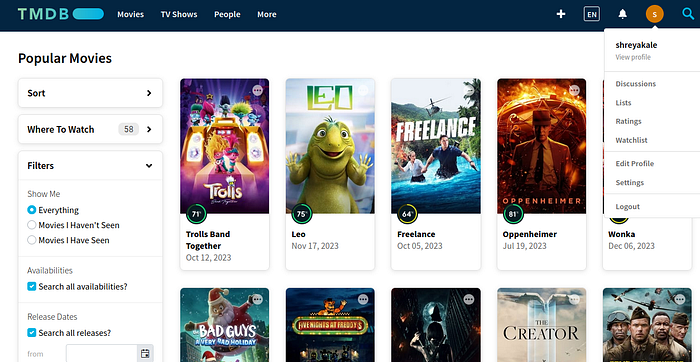
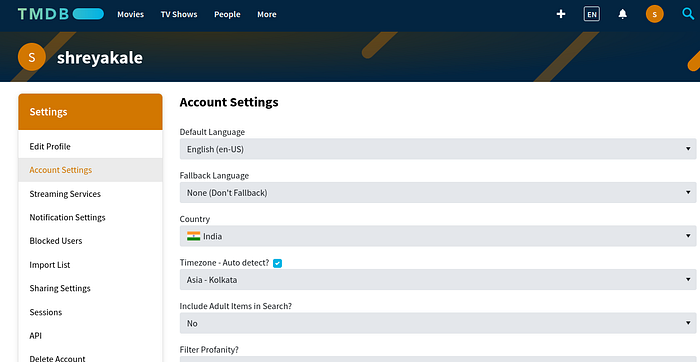
Let’s create an API key, By clicking on your profile and clicking settings.
Now click on API from the left side panel.
Click on Developer
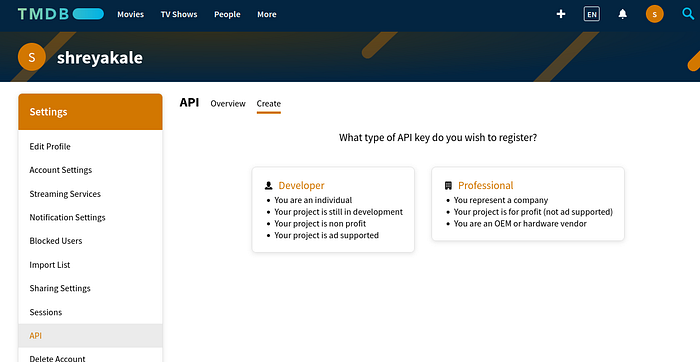
Now you have to accept the terms and conditions.